When you hear "IT asset disposal," you might just think of getting rid of old computers. But it's so much more than that—it’s a carefully planned process for retiring your company's technology safely and responsibly. A solid strategy isn't about just tossing out hardware; it's about wiping data clean, recycling electronics by the book, and even recovering money from gear that still has some life left in it. Handled correctly, it turns a potential headache into a genuine asset.
What Is IT Asset Disposal and Why Does It Matter?

Think of every server, laptop, and smartphone in your office as a locked vault, each one holding sensitive information. When it’s time to retire that equipment, you wouldn't just leave the vault on the sidewalk with the door wide open, would you? The disposal of IT assets is the formal process of decommissioning that vault. It means making absolutely sure every shred of data is destroyed for good before the hardware itself is recycled, resold, or discarded.
This isn’t just good housekeeping; it's critical. Retired devices are notorious for holding onto residual data—customer lists, financial records, internal passwords, you name it. If you don't handle it right, that forgotten data becomes a ticking time bomb.
The Growing Importance of a Formal Strategy
Having a formal IT asset disposal (ITAD) strategy elevates this process from a simple cleanup chore to a core part of your company's risk management and sustainability plan. Winging it is a recipe for disaster.
Without a real plan, businesses are just asking for trouble:
- Data Breach Risks: It only takes one hard drive that wasn't wiped properly to cause a massive data breach. The damage to your reputation and customer trust can be irreversible.
- Environmental Non-Compliance: Your electronics are full of hazardous materials like lead and mercury. Federal and state laws are very clear about how e-waste needs to be recycled, and the fines for getting it wrong are steep.
- Financial Loss: A lot of retired equipment, especially enterprise-grade servers and networking gear, is still worth something. A proper disposal process helps you cash in on that remaining value instead of writing it off as a total loss.
And this challenge is only getting bigger. The global IT asset disposition market is expected to hit a staggering $40.1 billion by 2035. This boom is fueled by technology changing faster than ever and increasingly tough e-waste regulations.
A professional ITAD strategy isn't just another business expense—it's an essential investment. It shields your organization from legal trouble and public fallout while demonstrating a real commitment to data security and environmental stewardship.
At the end of the day, a well-thought-out plan for the disposal of IT assets gives you peace of mind. It’s the assurance that your company’s data is safe, you’re meeting all your compliance obligations, and your old tech is being handled in a way that’s good for the planet. To learn more about the nuts and bolts, check out our deeper dive into what IT asset disposition involves.
The Real Risks of Improper IT Asset Disposal
Letting old IT assets pile up in a storage closet isn’t just a housekeeping issue—it’s a ticking time bomb. Think of a retired server or a stack of old company laptops as digital ghost ships. They might be out of commission, but they're still loaded with valuable, and often highly sensitive, cargo.
Without a professional disposal process, you’re basically leaving these ghost ships adrift, where they can easily fall into the wrong hands. The fallout isn't just a simple financial loss; it's a direct threat to your data security, brand reputation, and legal standing. Every forgotten hard drive is a potential backdoor to disaster.
This isn’t some line-item expense you can minimize. It's a non-negotiable investment in risk management that protects the very foundation of your business.
Data Breaches from Discarded Devices
The most immediate and damaging risk is the data left on retired hardware. Just hitting "delete" or doing a quick reformat is nowhere near enough to permanently erase information. Data recovery tools can easily pull that "deleted" data right back, turning a tossed-out hard drive into a goldmine for cybercriminals.
Imagine a healthcare provider upgrading its office computers. If those old machines are just sent to a local recycler without certified data destruction, they could still contain thousands of private patient records.
A sobering study once revealed that a shocking 40% of secondhand hard drives purchased online still contained personally identifiable information (PII) from their previous owners. It just goes to show how common it is for sensitive data to slip through the cracks.
An oversight like this can quickly spiral into a devastating data breach. The consequences hit you from every angle:
- Hefty Fines: Violating data privacy laws like HIPAA or GDPR can lead to fines that stretch into the millions.
- Reputation Damage: Once public trust is broken, it's incredibly hard to win back. A data breach can lead to lost customers and a permanently tarnished brand.
- Legal Action: You could find yourself facing expensive lawsuits from every single person whose data was exposed.
Environmental Compliance and E-Waste Regulations
Beyond the digital threat, there's a serious environmental one. Electronic devices are packed with hazardous materials that can wreak havoc on ecosystems if they’re just dumped in a landfill.
Your old IT assets contain a nasty cocktail of toxic stuff. Laptops, servers, and monitors are full of lead, mercury, cadmium, and flame retardants. When these materials seep into the soil and groundwater, they create environmental hazards that last for decades.
To fight this problem, federal and state governments have put strict e-waste regulations in place. The Resource Conservation and Recovery Act (RCRA) sets the national framework, and many states have their own specific laws dictating exactly how electronics must be recycled. You can learn more about the environmental impact of electronic waste and why these rules are so important.
Ignoring these regulations isn't an option and can lead to:
- Substantial Fines: The penalties for improper e-waste disposal are steep, especially for businesses with large amounts of equipment.
- Public Backlash: In today's world, people care about corporate social responsibility. News of environmental negligence can quickly turn into a PR nightmare.
- Legal Liability: Your company can be held legally and financially responsible for the entire cleanup cost if your gear is dumped improperly.
A formal ITAD strategy isn't just about checking boxes. It’s about building a resilient organization that protects its data, follows the law, and does its part for the environment.
How To Guarantee Secure Data Destruction
So, we've talked about the serious risks of getting IT asset disposal wrong. The next logical question is: how do you get it right? The first thing to understand is that securing your data is more than just dragging files to the trash bin. That's a rookie mistake. Doing that just tells the computer to "forget" where the file is, but the actual data is still sitting on the drive, ready to be recovered with simple, widely available software.
To truly protect your information, you need data sanitization. This is the process of permanently and irreversibly destroying the data on a storage device.
Think of it this way: deleting a file is like tearing the table of contents out of a book. The chapters are all still there; you’ve just made them harder to find. Data sanitization is like running every single page of that book through an industrial shredder until it’s nothing but confetti.
This isn't an optional step. It's the only way to be absolutely sure your company's sensitive information doesn't walk out the door on an old server or laptop hard drive.
As you can see, cutting corners leads directly to two outcomes you want no part of: crippling data breaches and hefty regulatory fines. Both can do massive damage to your bottom line and reputation.
Overwriting Data With Software Wiping
One of the most common and effective ways to sanitize a drive is through data wiping. This is a software-based method that works by writing over every single part of the storage device with random patterns of data. It essentially buries your original information under layers of digital gibberish.
The industry benchmark for this process is the DoD 5220.22-M standard. While the name is a mouthful, the concept is simple. The software writes a pattern of ones and zeros across the entire drive, then does it again with a different pattern, and finally completes a third pass with random data.
This three-pass process makes the original data practically unrecoverable, even with sophisticated forensic tools. It’s like painting over a canvas with three thick, opaque layers of paint—whatever was underneath is gone for good. This method is perfect for assets you plan to resell or reuse, as it leaves the physical hard drive completely functional while providing a certified, auditable trail of data destruction.
When To Use Physical Destruction
While software wiping is incredibly effective, some situations demand a more final solution. That's where physical destruction comes in. This means shredding, crushing, or completely disintegrating the storage device, making data recovery physically impossible. There's simply no coming back from this.
Physical destruction is the go-to choice in a few key scenarios:
- Damaged or Non-Functional Drives: If a hard drive is dead and won't even power on, you can't run a software wipe. Physical destruction is your only guaranteed option.
- Highest Security Needs: For organizations handling classified government data, top-secret intellectual property, or other ultra-sensitive information, shredding provides an unmatched level of security.
- End-of-Life Solid-State Drives (SSDs): SSDs store data differently than traditional magnetic hard drives. Wiping can sometimes leave behind recoverable data fragments in worn-out memory cells. Shredding eliminates that risk entirely.
It's important to remember that professional services, like those offered by New York data recovery specialists, can sometimes pull data from even damaged drives. This fact alone highlights why certified destruction methods are non-negotiable for any business. For a deeper dive, check out our guide on the best ways to destroy a hard drive.
Choosing between these methods can be tough, but a certified ITAD partner can help you develop the right strategy. To make it easier, here's a quick comparison of the two primary certified destruction methods.
Comparing Data Destruction Methods
This table breaks down the key differences between software wiping and physical shredding, helping you align the right method with your security needs, asset types, and goals.
| Method | Process | Best For | Security Level | Allows for Reuse? |
|---|---|---|---|---|
| Software Wiping | Overwrites existing data with random patterns (e.g., DoD 5220.22-M) | Functional hard drives, laptops, servers, and devices intended for resale or redeployment. | High (renders data forensically unrecoverable) | Yes |
| Physical Destruction | Shreds, crushes, or disintegrates the storage media into small fragments. | Non-functional/failed drives, SSDs, and assets containing highly classified data. | Absolute (makes data physically impossible to recover) | No |
Ultimately, the choice between wiping and shredding comes down to your risk tolerance, the condition of your assets, and whether you want to recover value from the old hardware. The right ITAD partner will assess each device and apply the most appropriate method, ensuring your data is protected without compromise.
Managing the Logistics of IT Asset Removal
Once you’ve nailed down your data destruction plan, the next challenge is actually getting all that equipment out the door. The operational side of the disposal of IT assets can look like a mountain of work, but the right partner can make it a smooth, secure, and fully documented process.
It all starts with a professional on-site pickup. A seasoned ITAD team shows up at your facility with the right gear and security protocols to handle the entire job. This could be anything from decommissioning servers in a live data center to packing out hundreds of old laptops from an office, all while causing minimal disruption to your daily business.
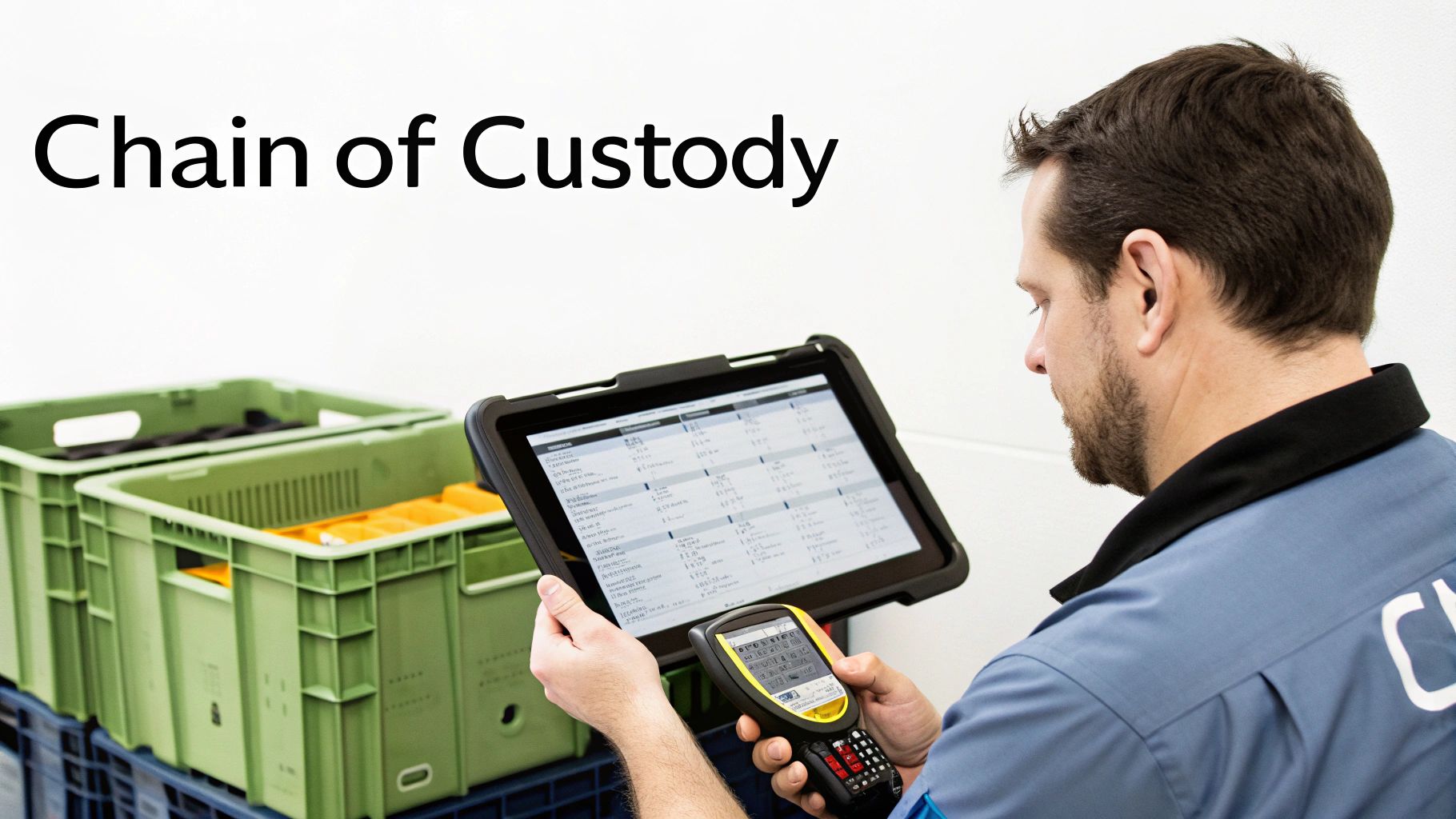
Securing the Chain of Custody
The moment a piece of equipment leaves your sight, its security becomes the top priority. This is where the chain of custody isn't just a piece of jargon—it's the most critical part of the entire logistical operation.
Think of it like tracking a valuable package from UPS. You get a tracking number and can see every scan and handoff until it’s delivered. A chain of custody for IT assets is the same concept but dialed up to an enterprise security level. It's a documented, unbroken trail that follows your gear from your office to its final destination.
The chain of custody is your verifiable proof that every single asset was handled according to strict security protocols. There are no gaps where a device could vanish. It’s the very foundation of a defensible and compliant disposal process.
This detailed documentation creates total accountability. Every technician who touches an asset, every truck it's loaded onto, and every secure facility it enters is logged. This transparent system eliminates the risk of equipment getting lost or stolen in transit and gives you complete peace of mind.
The Asset Auditing and Reporting Process
A key part of these logistics is the asset audit. As your equipment is being packed up or when it arrives at a secure processing facility, every single item gets individual attention. Technicians scan the serial number of every asset—from servers and hard drives to switches and monitors.
That scan feeds into a master inventory report, creating a detailed manifest of everything we collected from you. This report is more than just a list; it serves several vital functions for your business:
- Financial Records: It gives your accounting team the official documentation needed to remove the retired equipment from your company's fixed asset ledger.
- Compliance Verification: The report serves as hard proof for any auditors that all assets were disposed of correctly.
- Data Security Assurance: It lets you cross-reference your list of retired gear with the final certificates of data destruction, confirming nothing was missed.
This intense level of tracking is what separates a professional ITAD service from a simple junk removal. It turns the disposal process into a fully managed and auditable business function. You can see how Montclair Crew's comprehensive approach to IT asset removal delivers this kind of detailed oversight for businesses across the Atlanta area.
At the end of the day, managing the logistics of IT asset removal isn't just about hauling away old tech. It’s a security-first operation built to protect your data, keep you compliant, and give you an auditable paper trail from start to finish. When you work with experts who live and breathe chain of custody and detailed asset reporting, you can retire your technology with full confidence that every "i" is dotted and every "t" is crossed.
Turning Old Technology into New Revenue
So far, we've talked a lot about managing the risks and costs of getting rid of old IT assets. But what if that whole process could actually put money back into your budget? When you stop seeing old equipment as a liability and start seeing it as a hidden asset, the game completely changes.
This is where equipment remarketing comes into the picture. A lot of your retired IT gear is far from worthless—in fact, it often holds significant value on the secondary market. A true ITAD partner doesn't just haul away your old tech for recycling. They meticulously assess every piece for its resale potential, turning what was once a sunk cost into a fresh revenue stream.
This simple shift can transform an expense line on your budget into a welcome credit. It’s just a smart financial move that helps you get the most out of what you spent on technology in the first place.
Identifying High-Value Assets for Resale
Okay, so not every piece of old equipment is a diamond in the rough, but you'd be surprised how well many enterprise-grade assets hold their value. The first step to unlocking that cash is knowing what to look for, and an expert partner knows exactly what the secondary market is hungry for.
Here are some of the items that consistently fetch high resale prices:
- Enterprise Servers: Components like CPUs, RAM, and storage from big names like Dell, HP, and Cisco are always in demand.
- Networking Gear: Companies looking to expand their infrastructure without breaking the bank are constantly hunting for high-end switches, routers, and firewalls.
- Recent-Model Laptops and Desktops: Business-class laptops that are less than three or four years old can be easily refurbished and find a new home.
- Data Center Components: Sometimes it's not just the servers. Entire racks, power distribution units (PDUs), and other infrastructure can be sold off as a complete package.
Data centers are the perfect example of this model in action. They generate the lion's share of valuable retired assets, accounting for a massive 60.73% of the global ITAD market share. As more companies shift to the cloud, they're decommissioning entire server farms, which creates a huge opportunity for resale. You can get more insights on this trend and the value of refurbished servers by checking out the full research on the ITAD market at fortunebusinessinsights.com.
The Remarketing and Profit-Sharing Process
Once the valuable gear is singled out, a careful, methodical process kicks off to get the absolute best price. This is a whole lot more involved than just throwing an old computer up for sale online; it’s a professional operation designed to squeeze out every last dollar of remaining value. You might be shocked at how easy it can be to sell an old computer or other IT equipment when you have a specialist handling it.
The typical workflow looks something like this:
- Testing and Auditing: Every single component gets put through its paces to check its condition and functionality. We create a detailed audit that logs all its specs, model numbers, and serial numbers.
- Certified Data Destruction: This is non-negotiable. Before anything else happens, all data is permanently wiped using DoD-compliant methods, and you get a certificate to prove it. This keeps you secure while making sure the hardware can be used again.
- Refurbishment and Repair: We'll fix minor cosmetic issues and handle any necessary repairs to get the asset looking and working its best.
- Strategic Resale: Finally, the refurbished equipment is sold through our established network of buyers around the world, guaranteeing we hit the best possible market price.
A profit-sharing agreement is our transparent model where the net revenue from these sales is split between your company and us. This creates a powerful incentive for your ITAD partner to get the highest possible return on your assets.
This approach just makes sense—it aligns everyone's goals. Your partner is motivated to work harder for you, and you get a check for equipment that was just gathering dust in a closet. It turns IT asset disposal from a logistical headache into a strategic financial win.
Why ITAD Documentation and Certification Is Essential
Think the job is done once the truck pulls away with your old equipment? Not so fast. The disposal process is only truly finished when you have the official documentation in hand, proving every single step was handled securely and by the book. This paperwork is your legal shield and your final proof that you've met all your obligations.
It's a lot like selling a house. You don't just toss the keys to the new owner and walk away. You go through a formal closing, signing legally binding documents to transfer ownership and liability. ITAD documentation does the exact same thing—it formally closes the lifecycle of your assets and protects your company down the road.
Your Non-Negotiable Certificates
For every batch of equipment you retire, your ITAD partner absolutely must provide two key documents. Consider these non-negotiable. They are your definitive proof that the job was done right.
Certificate of Data Destruction: This is the big one for security. It's a legal document certifying that all data on your hard drives, SSDs, and other media was permanently destroyed, usually according to a specific standard like DoD 5220.22-M. Critically, it should list the serial numbers of the devices that were wiped, creating a clear audit trail from asset to erasure.
Certificate of Recycling: This certificate confirms all your non-working or worthless electronics were processed in an environmentally compliant way. It's your proof that you followed federal, state, and local e-waste laws and kept hazardous materials out of landfills.
These certificates aren't just for filing away. They're vital for internal ESG reports and for proving compliance with regulations like Sarbanes-Oxley. They are your official record showing you acted with due diligence.
Vetting Partners Through Industry Certifications
So, how do you know a vendor is actually going to do what they say they will? The answer is third-party industry certifications. These credentials prove that a provider has been independently audited and meets the highest standards for both data security and environmental responsibility.
When you're picking a partner, look for major certifications like R2 (Responsible Recycling) and e-Stewards. These aren't just fancy logos for a website; they represent a serious commitment to secure, ethical, and environmentally sound practices.
The global e-waste problem is getting worse, not better, which makes certified disposal more important than ever. The ITAD market itself is expected to explode from USD 25.31 billion in 2024 to USD 54.54 billion by 2030, mostly because of tougher regulations. If you want to dive deeper into these trends, Custom Market Insights has some great data.
Choosing a certified partner is simply the smartest way to vet a vendor. It ensures your old equipment is handled by a company that has invested in the right processes and security to protect both your data and the environment, giving you complete peace of mind.
How to Choose the Right IT Asset Disposal Partner
Picking the right partner for your IT asset disposal is probably the most important decision you'll make in this whole process. Think of it like hiring a crew to decommission a secure facility. You wouldn't just hire the cheapest guys you could find; you'd demand a team with proven expertise, airtight security, and a spotless track record.
Your ITAD partner is the final gatekeeper for your company’s sensitive data and brand reputation. Choosing a vendor based on price alone is a rookie mistake that can lead to catastrophic data breaches and painful legal fines. The real goal is finding a partner who delivers a complete, transparent, and compliant solution from start to finish.
Core Pillars of a Trustworthy ITAD Partner
To make a smart decision, you need to measure potential vendors against four essential pillars. These are the non-negotiables that prove a partner can handle the job with the security and professionalism your organization deserves.
A truly reliable partner won't just be good at one or two of these—they'll master all of them.
- Security Standards: They must offer certified data destruction methods like DoD 5220.22-M wiping and physical shredding. More importantly, they need to provide auditable proof for every single device they handle.
- Compliance and Certifications: Keep an eye out for key industry certifications like R2 or e-Stewards. These aren't just fancy badges; they are third-party proof that a vendor's processes meet the highest environmental and data security standards.
- Logistical Excellence: A top-tier partner manages the entire process flawlessly. This means secure on-site pickup, a strict chain of custody from your door to theirs, and detailed asset reports you can actually understand.
- Value Recovery Model: They should have a transparent process for sorting out valuable assets, refurbishing them, and sharing the resale revenue back with you. This turns your old tech into a welcome financial return.
Questions to Ask Potential Vendors
Once you've got a shortlist of certified partners, it's time to start digging. Asking the right questions is how you separate the talkers from the doers. Treat this like an interview for a critical role in your company, because that's exactly what it is.
Use this checklist to guide your conversations and compare your options head-to-head.
- Can you provide a sample Certificate of Data Destruction and a Certificate of Recycling? Seeing their actual paperwork tells you everything about their level of detail and professionalism.
- Walk me through your chain-of-custody process. Ask for a sample report or a step-by-step explanation of how they track an asset from pickup to final disposition.
- How do you decide what gets remarketed versus what gets recycled? A good partner will have a clear, data-driven system for assessing the value of your old equipment.
- What's your profit-sharing model for resold assets? Make sure the terms are crystal clear, fair, and transparent, with no hidden fees waiting to surprise you.
- Are your facilities and technicians certified (e.g., R2, e-Stewards)? Don't just take their word for it—ask to see proof of their current certifications.
Understanding the top 10 outsourcing benefits can really shape your decision here, as many of those advantages apply directly to working with a specialized ITAD service.
Choosing a local partner who gets the regional compliance landscape can be a huge plus. A Metro Atlanta-based company, for example, will already know Georgia's specific e-waste regulations inside and out and can offer much more responsive, flexible service for on-site needs.
At the end of the day, the right ITAD partner makes the entire process simple, shields your organization from risk, and helps you hit your financial and sustainability targets. By asking these tough questions, you can confidently pick a vendor who acts like a true extension of your own team.
Ready to simplify your IT asset disposal with a trusted, local partner? Montclair Crew offers comprehensive, certified, and secure ITAD services for businesses all over Metro Atlanta. We protect your data, guarantee compliance, and work to get you the maximum return on your retired equipment. Contact us today for a seamless and responsible solution at https://www.montclaircrew.com.